This document will show how security is implemented using role, group and function
including setting up the necessary scripts along with providing examples.
Table of Contents
Create Roles¶

- In portal_categories/role define roles needed (our security policy will be based on roles).
- Create a role that can add new elements (purchases, payments, etc).
- Create a role that can consult/view elements.
Add Functions¶

- In portal_categories/function select action Add Category.
- Create two functions with explicit Id, Title and Codifaction
- Example: accountant, Accountant, ACC
Add Users and Assignments¶

- In person module, create new persons with assignment, and valid login.
- In the assignment, set the function of the assignment according to the permissions you want to allow for the given user.
- Don't forget, a person without a login, a password and an open assignment will not be an user.
Fixing Assignment Lookup Policy¶
In our example we only use the function to determine the rights of a user.
The default is to base on user rights on site and group, too (see getPortalAssignmentBaseCategoryList).
To override this default, we need to create a Python script named (to follow the
naming conventions) ERP5Type_getSecurityCategoryMapping¶ in portal_skins/custom
(or any other folder in the acquisition path) with this content:
## Script (Python) "ERP5Type_getSecurityCategoryMapping"
##bind container=container
##bind context=context
##bind namespace=
##bind script=script
##bind subpath=traverse_subpath
##parameters=
##title=
##
return (
('ERP5Type_getSecurityCategoryFromAssignment', ['function'] ),
)
Setting Access For A Given Type¶
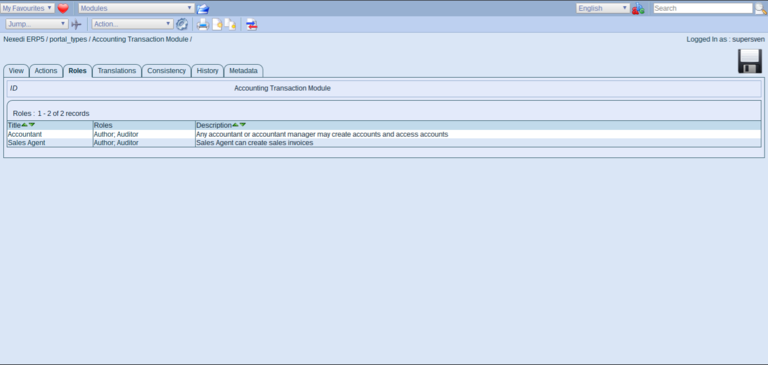
Next we want to restrict access on the Accounting Module. Call
accounting_module/Base_setDefaultSecurity to disable security acquisition
for the module and then go to portal_types/Accounting Transaction Module/manage_editRolesForm
(the Roles tab of the management interface of the Accounting Module Portal Type)
Add Roles For This Module¶
- Name: Accountant
- Role: Assignor
- Base Category¶ Script: ERP5Type_getSecurityCategoryFromAssignment
- Category¶: accountant
This will set the Assignor role to any person with an assignment specifying the
accountant function. Once every role definition is added, select Update Local Roles
from the actions tab to make sure, the new roles are applied.
Repeat this process for every portal type you need.
To verify things worked, try log in with one of the newly created persons
using the associated login/password pair and check whether accounting transactions
are visible.
Note that if you already had data in your ERP5 instance, you also need to
reindex the ERP5 site after managing roles. Otherwise users will have access to
objects, but these won't display in listboxes as they are not represented in the catalog
in relation to the newly changed roles.
Extending Security A Bit Further¶
Roles are assigned on a per-type basis and not on a per-object basis. This allows
you to set generic rules across all kinds of objects and once they are set, you don't
have to change the security settings anymore.
Category¶
This is the category the user must have to get access permission (like function/ceo)
ERP5Type_getSecurityCategoryMapping¶
This script tells ERP5 which base category will be used for setting the security policy.
You must return every base category list you want to use in the Base Category setting.
If you want to grant access based on the location-site OR on based on group and function,
you'll have something like that:
return (
('ERP5Type_getSecurityCategoryFromAssignment', ['site'] ),
('ERP5Type_getSecurityCategoryFromAssignment', ['group','function'] ),
)
Base Category¶
Denotes a list of base categories (space separated) that should correspond
to an entry returned by EP5Type_getSecurityCategoryMapping. When a user
creates an object, ERP5Security takes the Owner's assignments and sets permissions to
people with the same base category.
Base Category¶ Example
If you set a Base Category = group and Category = function/ceo,
then the permission will be attributed to the CEO of the Owner's assignment's
group. If you omit the Category, only the Owner's properties will be taken into
account. If you omit Base Category, the rule will only be based on the
specified category (in general, a function). Note that you also specify
a list of Base Categories and Category separated by spaces.
Related Articles¶